802.11 1mbps 2mbps dsss
FHSS frequency hop will hop from 1 to 2 so doubles the bandwidth.
802.11b 11mbps uses 11 channels
802.11a 54 Mbps 13 channels on UNII not compatible with 802.11b
802.11g 54 Mbps ISM compatible with 802.11b
802.11N can run on both 600 mbps MIMO multiple in multiple out and OFDM to send the data.
ISM uses 900 2.4 and 5.5 only 2.4 is used for 802.11b g n
UNI uses 5.0 ghz and is for 802.11a and 802.11n
1 6 11 do not overlap.
SSID is used, this is similar to a VLAN to segment the networks.
CSMA /CA collision avoidance.
WEP is insecure
WPA allows you to add security 802.1x and AES
MAC adresses can be spoofed.
EAP-FASt Flexible authentication can be used for the connection.
VPN IPSEC can be used to segment the traffic to the HQ.
802.1x uses EAP and Radius to verify your access.
LEAP uses a radius and 802.1x
Cisco
IDS and firewall to control the traffic.
Cisco UWN unified wireless network.
Client devices laptop
accesspoints cisco AP
Network unification like QoS IPS RF management all of this is done by the controllers.
network management can be done using the WCS server
Mobility services like guest , Voice , threat detect.
benefits.
reduce TCO
enhance visibility
manage the RF (cleanAir)
Security Controller
Unify the wire and wired-less
enhance collaboration.
LWAPP is what the APs use in order to connect to the controller.
AP to WLC
Layer 2 LWAPP controller must be on the same subnet Ethertype 0xbbbb
Layer 3 LWAPP controller can be on a different subnet. 12222 12223
12222 data 12223 control
CAPWAP is the newer one.
Uses AES to secure the com
MTU discovery
Control 5246
data 5247 so the opposite
Split MAC - Lwapp
the AP does
Beacon 802.11
802.11 control
802.11e queue and piroritization
802.11i encryption
The Controller does.
802.11i security
802.11 mac management
802.11e reserve resources.
Local MAC - CAPWAP
802.11 MAC management so the AP does this instead of the controller.
Controller can also proxy.
AP modes
Local Mode - the usual
Hybrid - it will reside across the WAN H-REAP
Monitor - cycle every 60 and do not participate. Used for IDS. Location based.
Rogue Detector - sits on the Trunk and checks if there is a rogue device
Sniffer mode- captures packets and sends them to a Sniffer Airopeak.
Rogue detector gets a list of MACs they hear from other devices.
If that MAC is on the WLC then the rogue detector will let you know.
Bridge mode is for MESH
Connection Lwapp.
Send Lwapp Discovery.
1. local subnet
2. Get WLC from other AP
3. previously stored WLC address.
4. DHCP option 43
5. DNS CISCO_LWAPP_CONTROLLER.local.domain.
WLC will answer
AP gets list of WLCs
Selects AP
1. Previously configured.
2. Master
3. most available.
AP to WLC join
Capwap
does capwap
no response 60 seconds does LWAPP
no response start again.
First
Second
Tertiary
Master
most available.
Supplicant is the client.
WLC is the authenticator
Radius is the Authenticating server.
To WLC is capwap
from WLC to Radius is EAP extensible authentication protocol.
EAP- TLS public key.
EAP - TTLS certificate only on the server.
PEAP - Cisco + mschap.
LEAP - Cisco plus the CCX extensions.
EAP-FAST build a tls tunnel
WLAN is an SSID
Interface maps the VLAN to the SSID
port is a port.
A port goes to the switch
you can use many ports and etherchannel them.
Management interface. - Used for L2 Lwapp. Connection to radius. In-band management
Service port - used for out of band management. Statically configured.
AP manager - L3 discovery static
Dynamic interface - is to map the VLAN to WLAn
Virtual interface - DHCP relay , mobility
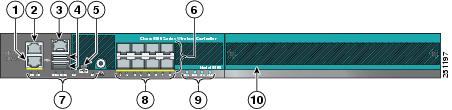
So port 2 is a physical port.
You configure it as the SERVICE port. It is for out-of band management.
Ports 8 can be aggregated LAGed and will go to a switch.
Sorry, best I can do.
Service Port. is a totally separate port for out of band servicing.
Management port is the in band and old Layer 2 LWAPP.
AP manager is for Layer 3 LWAPP.
Dynamic ones are for each VLAN WLAN they will change dynamically.
Virtual is to connect to another WLC and transfer mobility. So you can ROAM from room to room or building.
2100 25
ISR 25.
So far easy.
3750 Switch with contorller built in 50
4400 100
6500 WLC module 300
5500 500
Intracontroller
ie the same controller.
So no chaneg except you moved IPs.
Inter controller Layer 2.
From one controller to the next
Just moves the MAC from WLC1 to WLC2 database.
A mobility message updates the controller.
Inter controller Layer 3.
From one IP subnet to another.
WLC 2 Creates a shortcut. An ANCHOR and tunnels the data back to WLC1.
Mobility group will create the anchor and tunnel.
Up to 24 WLC s
UDP 16666 unencrypted
UDP 16667 encrypted.
Minimize intercontroller roaming.
less than 10 ms
Layer 2 is better
Detrministic redundancy
Primary secondary tertiary.
Dynamic
Easy and load balance.
N+1 one controller is backup
N+N same number of controllers as the ones you have deployed.
N +N + 1 same number of controllers as you have + tertiary as spare.
Limit to 20 users
7 voWLAN
RRM radio resource management
Adjust RSSI
balance the clients
RF group is a group of WLC that sync their RRM
80 signal will elect a master to set up the strenght
Neighbor messages
EoIP for guests
All the guest traffic goes to one WLC. an anchor WLC.
Mesh
RAP is Root
MAP is not connected to the wire
Four hops max of 8
throughput drops every hop by 50%
20 MAP per RAP max of 30
1100 internal 3500i internal
1200 3500E external
branch
300 ms or less
use H-REAP for WAN
LOCAL mac
allows you to work even if the WAN is down.
REAP
extends lwapp timers.
Layer 2 security limit
H-REAP
Allows NAT


No comments:
Post a Comment